Most organizations believe the subsequent stage of improving their security posture means adopting a Next-Generation Anti-Virus (AV) or Endpoint Detection Response (EDR) tool.
AV and EDR technologies are used to protect endpoints from attack but are merely just one measure of security. Having an EDR tool installed in your network does not mean that you are totally secure. A seasoned attacker will inevitably be able to find a way to bypass tools like this, especially if the tool is left unmonitored, not updated and/or misconfigured EDR, threat actors may further leverage advanced techniques such as a credential grab to circumvent these endpoint safeguards.
To truly strengthen your security posture, an organization must consider Managed Security Services in conjunction with tools like AV and EDR. By adding management and monitoring, you are adding an extra layer of protection to your system. Not only does your system have the detection tool installed, but now you have a human operator checking the prompts from the system, making sure that action can be taken as soon as a threat has been identified and ensuring that all tools are as up to date as possible.
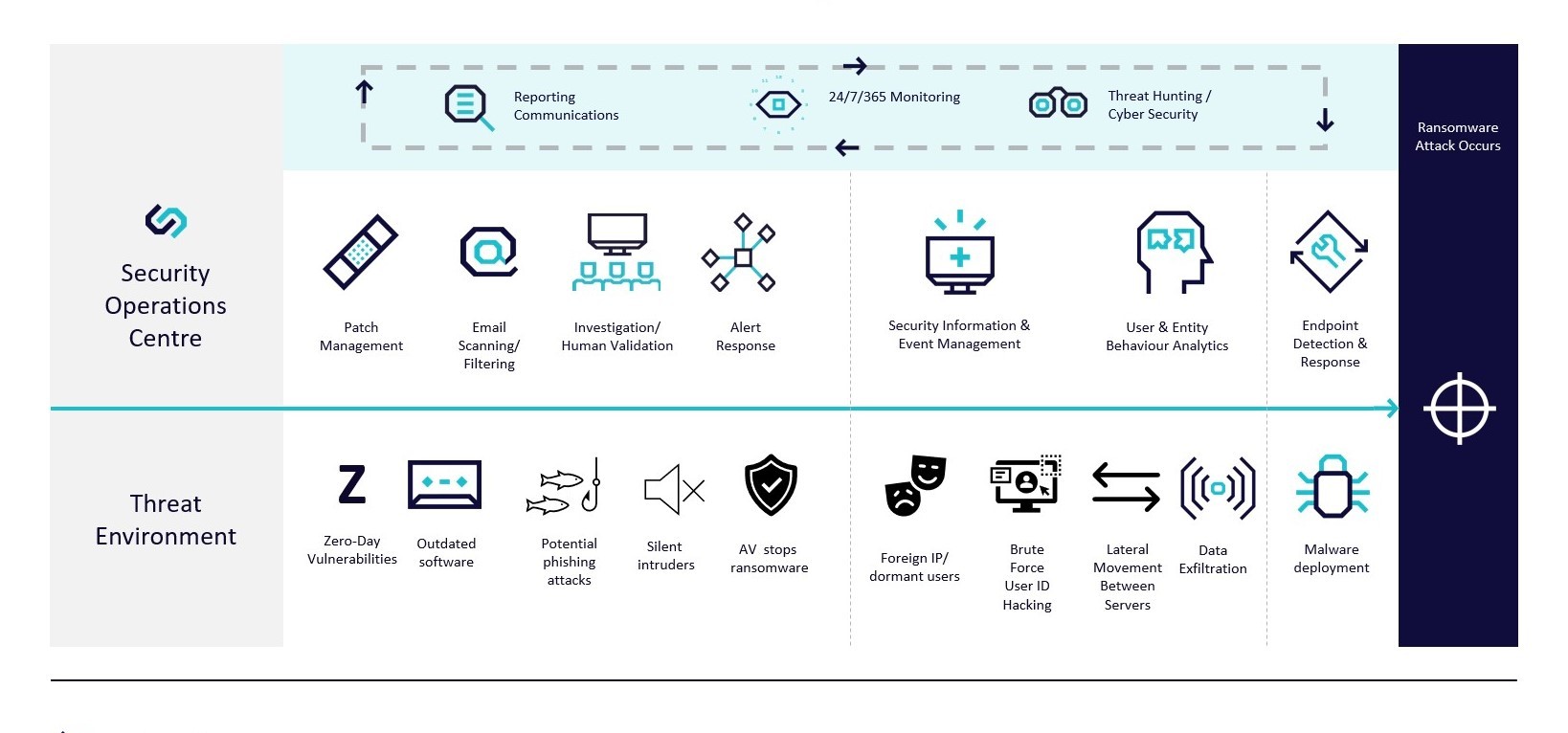
To demonstrate, we’ve compiled an overview of a ransomware attack that our forensics team deconstructed to analyze how it could have been prevented before the ransomware was deployed (the point of the attack).
By looking at the Indicators of Compromise (IOCs), we can see how different tools work together and how important it is that those tools are managed and monitored effectively to prevent an attack from occurring.
1. Endpoint Detection & Response (EDR)
In this case, the client did not have an EDR tool installed on their system, instead, they were relying on a typical security setup of an Anti-Virus (AV) tool and perimeter firewalls, which allowed the ransomware attack to be successful, encrypting all servers, including their backups.
Had a properly configured and monitored EDR tool been installed on their network, it would have identified the malicious process on execution, alerted the Security Operations Centre (SOC), killed the process, and quarantined that device.
While a monitored and managed EDR tool would have stopped the deployment of ransomware, what about the events that led up to this ransomware deployment?
2. User & Entity Behaviour Analytics and Security Information & Event Management
CyberClan’s SOC coupled with Security Information & Event Management (SIEM) and User & Entity Behaviour Analytics (UEBA) platforms would have identified security events and led to a further investigation from one of our round-the-clock Security Analysts.
During the investigation, several security events were identified as having occurred prior to the ransomware deployment. With a managed and monitored SOC that deploys both a SIEM and UEBA platform, these security events would have been flagged and further investigated. In this case, our team identified the following security events:
- Lateral movement between servers is when movement between multiple devices on the network occurs.
- A Brute Force Attack was attempted as an attacker used a combination of passwords and/or usernames to force access into the system.
- Multiple failed logins, because of the brute force attack, went unnoticed.
- Unusual and foreign IP addresses were used to gain unauthorized access to a user profile signaling malicious intent.
- A dormant user account was accessed and used without notice.
3. Patch Management
Another common entry point for a Threat Actor, and the most likely entry point in this instance, is via the exploitation of outdated software.
A patch management solution will help to keep a network’s software and devices up to date and therefore minimize the potential gateways, outdated software, and devices provide into your environment. Note the most recent SolarWinds hack has been attributed to automated updates, another reason human monitoring and management is so important.
4. Alert Response & Investigation and Human Validation
Having a 24/7 managed service gives the peace of mind that someone is always monitoring your systems and will pick up on an alert when it comes in and investigate the root cause before damage is caused to the network no matter what time it occurs. Typically, Threat Actors will wait for a time when they feel they are less likely to be detected and then commit malicious actions.
5. Email Security Scanning/Filtering
It is commonly seen that an attacker gains access to user credentials through Phishing emails, meaning that email security and filtering is an essential tool to help minimize this threat.
CyberClan’s monitored and managed Email Security tool uses advanced AI technology to provide email security such as:
- SmartPhish Anti-Phishing
- Account Takeover Protection
- Configuration Security
- URL Clicktime Protection
- Policy Enforcement
- Shadow IT
- Malware Sandboxing
- Data Loss Prevention
- Encryption for Office 365
By now the gravity of how many missed opportunities to catch the Threat Actors at work prior to ransomware deployment are surely warranting a second look at Managed Security Services, but this all sounds so expensive!
A secure network and systems are the price of doing business these days. Consider the fact that over 60% of all small to midsize enterprises go out of business within six months of a cyber attack. Or, think about the average cost of ransomware attacks these days can range from thousands to millions, never mind the reputational cost to your brand, and potentially even regulatory issues that may come up as a result of not protecting your business.
While many organizations may not explore managed and monitored security services, working with an organization like CyberClan, that offers SOC-as-a-Service in a repeatable and scalable way can greatly reduce overhead while gaining the resources needed to keep your business secure which you are a company of 10 devices or a network of 10,000.
As demonstrated by the case study deconstructed above, a silent intruder poses threats of data exfiltration and fraudulent activity even before they ever deploy malware. Therefore, every organization needs to consider their legal and regulatory obligations. Having a 24/7/365 monitored and managed SOC that utilizes tools and platforms such as SIEM, UEBA, EDR, patch management and more will demonstrate your company’s overall due diligence regarding the security of the data and environment in which you do business.
The ever-evolving threat environment and changing regulatory obligations require a pro-active approach to cybersecurity. Cost-cutting and ignorance of the regulatory environment are no longer a successful defence.
To find out more about the solutions that CyberClan can provide to your business or institution, please contact us: US/CAD 1855 685 5785 or UK 0800 048 7360 or email us at info@athynhfojv.onrocket.site for more information.