Written by Slade Kai
Cyber-attacks are on the increase and a continuous threat to the digital space. The implementation of password management policies for your business is an integral component of security posture refinement.
Why Use Password Managers?
Password Managers such as 1Password, Dashlane, or LastPass utilize a centralized encrypted security vault to store login credentials. When a user visits a site or is prompted to enter their username or password, the Password Manager allows users to generate, store, and manage their credentials. Users only need to remember one master password to access their service vault and, in some cases, an additional Secret Key.
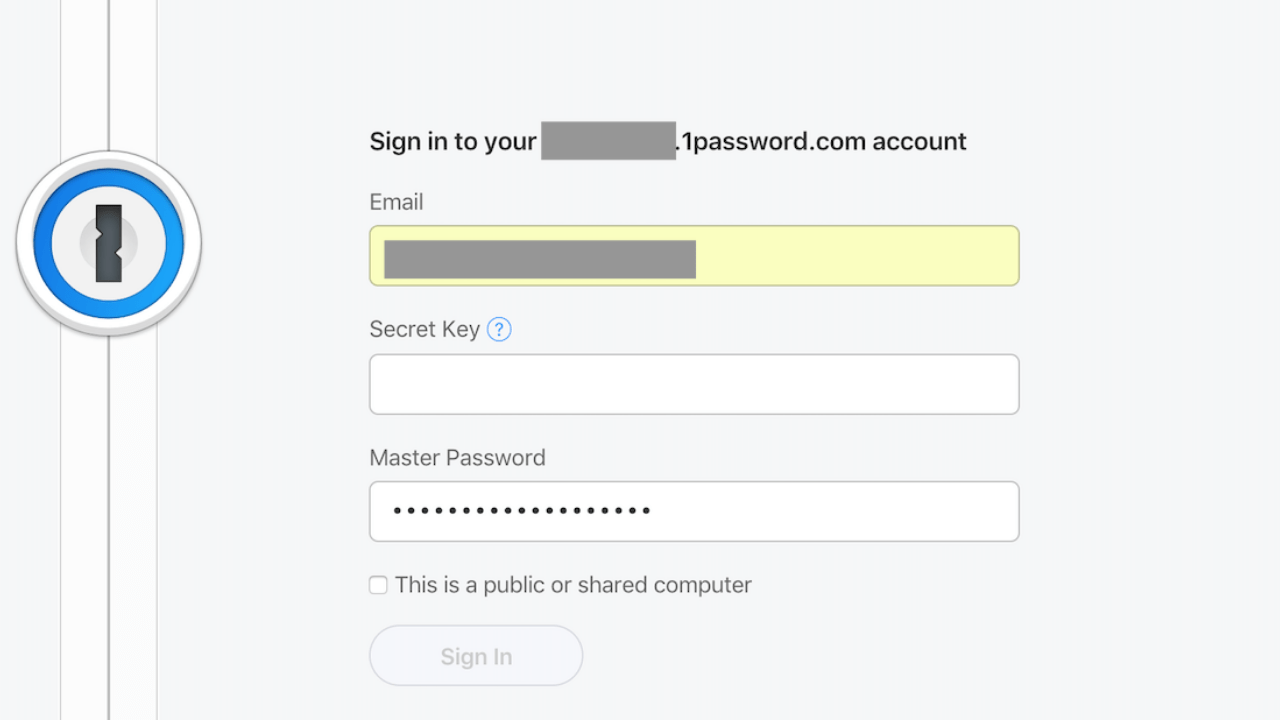
The Password Manager auto-populates your login name and password and allows the storing of important documents or other pertinent information like credit cards, personal health records (PHR), or personally identifiable information (PII). Additionally, some Password Managers offer additional security services such as dark web monitoring. Your security vault is scanned for any potentially compromised credentials, and you’re notified using the embedded logging and auditing functionality.
Let’s be honest, people, in general, are rather lazy. Laziness can lead to bad habits and being vulnerable to attack. It is not uncommon for employees to leave post-it notes on their desktop, share passwords with colleagues, or use the same password for personal and work accounts.
69% of employees have shared their passwords with colleagues. – Betanews
51% of people have the same password for their work and personal accounts. – Dataprot
SC Magazine reports that 93% of at-home workers admit to reusing passwords across accounts, a highly risky practice that leaves their employers vulnerable to breaches if their personal accounts are hacked.
Credentials can be exploited through several hacking techniques, such as brute force attacks, credential stuffing, and hash cracking. By combining traditional passwords with more advanced authentication technologies, such as biometrics and multi-factor authentication (MFA), these attacks can be greatly reduced. Microsoft reports “Multi-factor Authentication blocks 99% of all password safety issues.” Popular hardware authentication devices like Yubikey can simplify the MFA experience and be seamlessly paired with vendors such as Dashlane, LastPass, and Keeper. This provides administrative control for management teams.
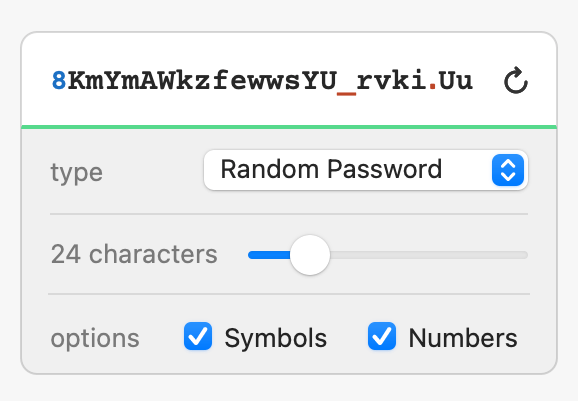
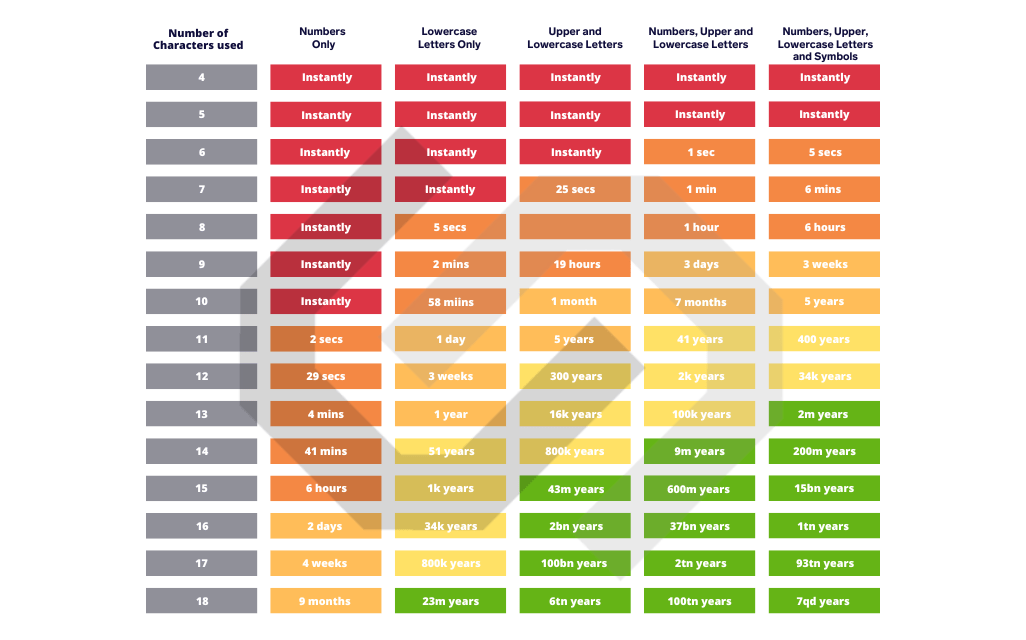
Password policies and the integration of special characters, length and complexity play a vital role in risk mitigation. Password Managers allow the customization of secure credentials based on company requirements. (See an example from 1Password)
Businesses work furiously to secure their networks in response to the increasing threat of cybercrime. Recent reports show weak or stolen passwords are responsible for 81% of data breaches, making them a big security concern for any company. The weaker the passwords, the easier it is for threat actors (TA) to gain access to your systems and cause destruction. Businesses that implement and apply best practices can alleviate unethical and fraudulent activities.
(The chart below demonstrates how effortless it is for TA to brute force your passwords)
Phishing schemes can be extremely effective for compromising systems. Without training or awareness, employees can easily be fooled into clicking on malicious links, resulting in the theft of login credentials.
Fortunately, password managers can verify if the URL is legitimate, preventing the username and password fields from being populated. Utilizing password managers that sync to the cloud, users can log in from a multitude of platforms such as computers, tablets, and mobile devices.
Business teams can collaborate and securely share passwords when accessing required web forms or Software-as-a-Service (SaaS) applications.
Most web browsers include the option for saving and auto-filling credentials. Although this may seem like an obvious choice, it’s discouraged and puts your environment at risk. Alternatively, IT policies can be implemented to include the installation of Password Manager browser extensions that allow end-users to securely access Password Manager vaults. The integration of Identity Providers such as ADFS, Jumpcloud, or Google Workspace simplifies account administration and overheads. The onboarding of staff can be automated by implementing policy-based account provisioning.
IT visibility is an essential component of any security blueprint. Adopting the common practice of remote work strategies, it’s even more crucial to establish a securely controlled environment. Password Managers allow for role-based access control (RBAC), monitoring accounts for unusual activity, and restricting employees’ permissions based on IT security policies.
Risk Mitigation
While the implementation of a password manager is strongly recommended as part of your security strategy, it does not come without some risk.
Management teams can educate staff on the use of Double-Blind Password or Horcruxing techniques. As the name implies, this refers to a secure method of storing passwords within a Password Manager that keeps the password hidden from both the Password Manager and the user. Essentially, you are splitting the password into two parts, the password manager and in your head. The horcrux adds an additional layer of security that only the user can unlock. Think of it like 2FA.
BEFORE: (Saved in the password manager)
username: slade
password: letsgofishing@^&
AFTER: (Added to the password field)
username: slade
password: letsgofishing@^&-Th1sway
horcrux is -Th1sway
In conclusion, ensure you do your research and choose a vendor that qualifies for your business requirements. Store a copy of Master passwords and secret keys in a bank’s safe deposit box. Increase your level of security by enforcing MFA, biometric technologies, and adopting the idea of hardware-based authentication with public-key cryptography.